Our Products
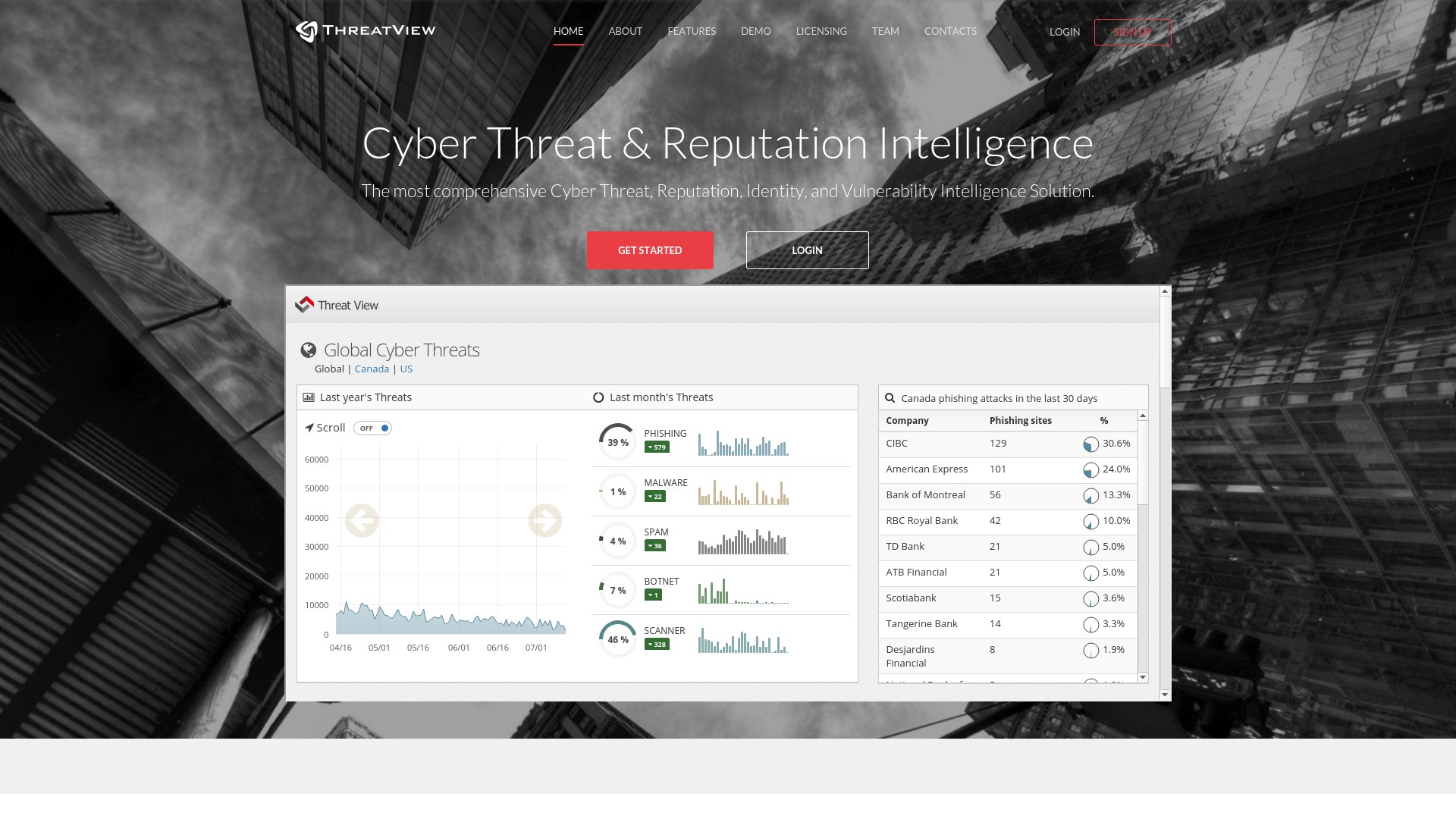
ThreatView
RiskView offers a comprehensive cyber threat intelligence and reputation management solution called ThreatView. ThreatView collects and analysis dark-web information including more than half a billion social posts; more than 20 million mobile applications; and millions of underground cyber communities discussions, security breaches, spams, vulnerabilities, and images to build a predictive intelligent prioritization engine. ThreatView helps organizations detect, analyze, and mitigate cyber threats and reputation attacks, while threats are still being developed. ThreatView leverages advanced Big Data technology, such as Hadoop, Machine Learning, Social Media, and advanced Crawling algorithms, to allow for early cyber threat detection.
Moreover, ThreatView continuously monitors millions of URLs, mobile applications, social media posts, zero day vulnerabilities, underground hacking communities, and third party vendors and their historical breaches. ThreatView also uses automation to analyze this massive amount of information. After it detects a relevant threat to one of your assets, the tools will immediately notify you. ThreatView’s security consultants analyze all relevant threats. Once a threat is confirmed after an investigation, security consultants take action to mitigate the threat in order to reduce its effectiveness. The tool also uses heuristic and machine learning algorithm to constantly evolve and get better at detecting relevant threats.
For complete details on ThreatView’s features and functionalities, see ThreatView Introduction or visit www.threatview.ca.
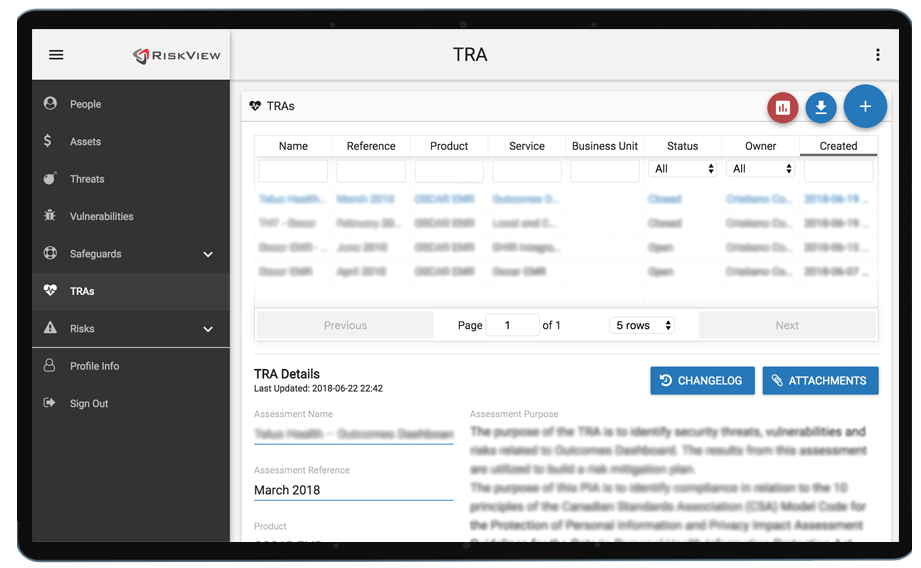
Harmonized Threat Risk Assessment (H-TRA)
RiskView offers a software as a service called Harmonized Threat Risk Assessment (HTRA) solution. This solution is built upon the Harmonized Threat Risk Assessment Model recommended by the government of Canada (see link… PDF) and has the following key features:
- Simplifies and automates the HTRA process, including information gathering,
- Automates the risk calculation,
- Facilitates issue tracking and reporting.
The solution is highly secure and supported by two-factor authentication
Register for a free account at: www.H-TRA.ca